I’ve never really used this very much, I mean I have it installed on my work laptop since I do work for GitHub. So I thought it’d give it a try. This post isn’t anything in depth, in fact mostly a reminder for me in the future or maybe it’ll be helpful to someone that stumbles across this posting.
GitHub CLI can be installed on a number of OS’s. The issue I ran into that prompted me to write this was how the gh cli tools authenticate with your account. On a system where you have a desktop (Windows, MacOS, or something like Ubuntu) (ie: not a headless system), when you first run the tools you’ll be prompted to connect with your browser to authenticate.
When the browser opens you’ll be prompted to allow access to your GitHub account. Once you accept you’ll be returned and can carry on with whatever you were doing.
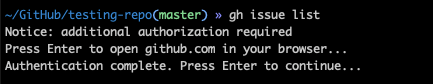
However, I run a lot of headless systems, the result I had when trying to run the command line tools was:

Hm, ok, there must be some other method of authentication. Off to the manuals I go to look. Nothing was found 🙁
I had to the open issues, surely someone has had the problem before, bingo, I found an open issue this reply by @mislav provides the answer. Create a file called ~/.config/gh/config.yml
hosts:
github.com:
oauth_token: TOKEN
user: YOUR-GITHUB-USERNAMEYou will need to generate a Personal Access Token (PAT), it doesn’t really say what scopes should be selected. I went with all the repo options and I also selected gist as there is a discussion that working with gists will be looked at in the future. Once created, paste the token into the ~/.config/gh/config.yml

You can copy this file to the rest of your machines instead of generating a new PAT for each machine, however, from a security side I could see a valid argument of having a different PAT for each machine. Should an account be compromised on a machine you could simply revoke that one PAT and not have to change every machine.
I hope this helps anyone that finds it.
